Bug Bounty & Vulnerability Threat Research Report
Measure, validate, and reduce exploit exposure across your production environments. A 2026 benchmark report on what really drives breach risk and remediation effort.
%20(3).webp)
Backed by the experience of these trusted brands
























































Why Exploit Exposure Persists in 2026
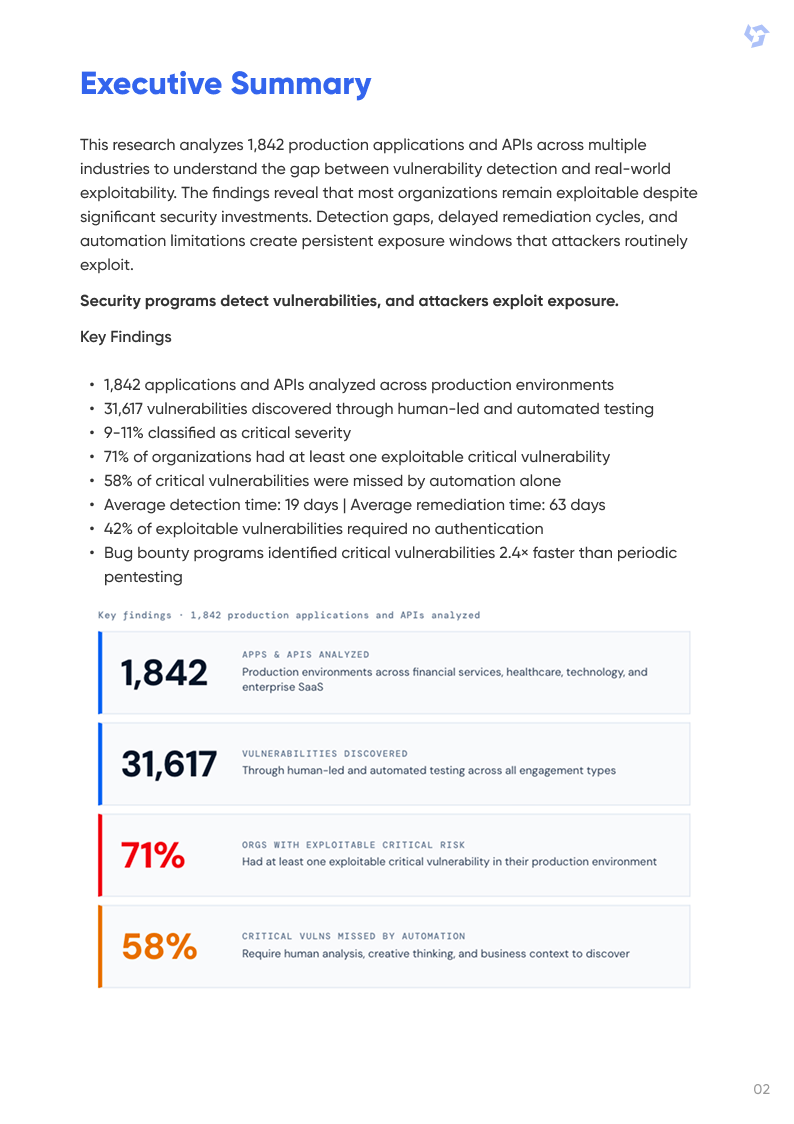
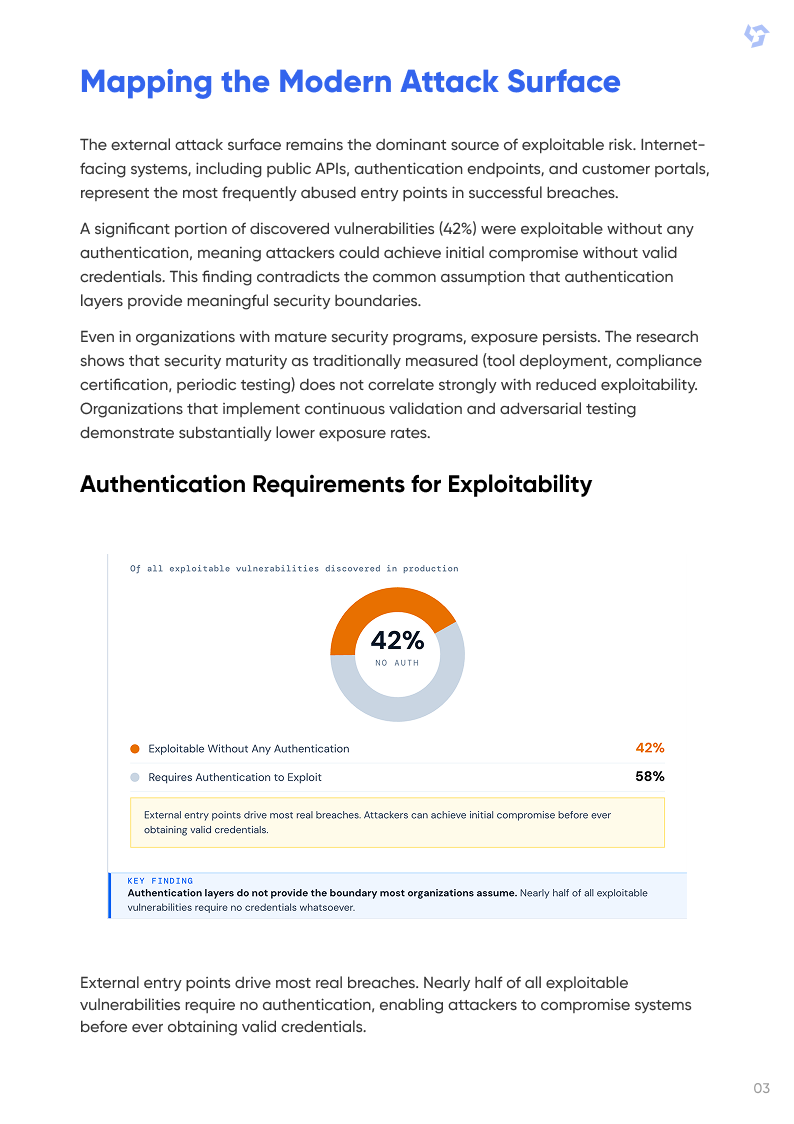
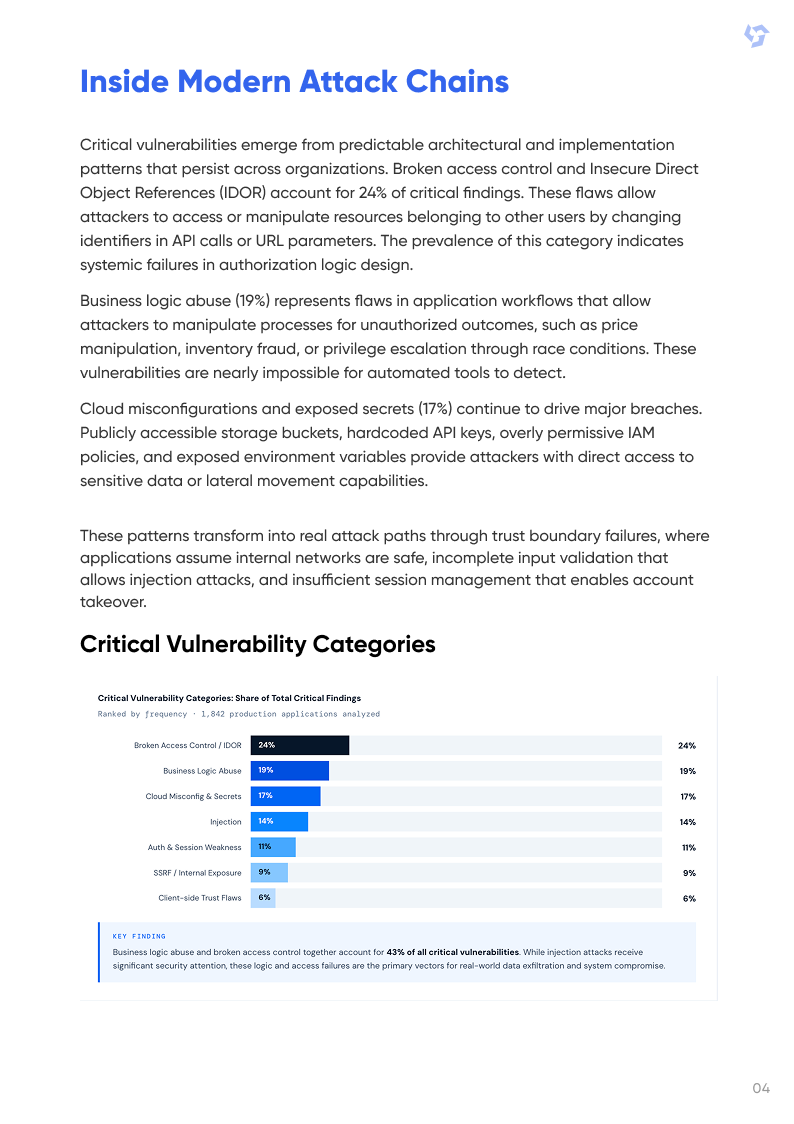
Despite significant security investments, most organizations remain vulnerable to attacks. AppSecure research across 1,842 production applications and APIs shows that detection gaps, delayed remediation, and automation limitations create persistent exposure windows that attackers routinely exploit.
This report explains how specific vulnerability types, attack paths, and operational practices disproportionately increase exploit risk and provides a framework for actionable risk reduction.
Key Insights Included in the Report:
- The Maturity Gap: 72% of applications passed compliance checks yet still exposed exploitable runtime risk due to limited contextual validation.
- Pre-Production vs Production Risk: 64% of gaps originate before production, while 81% of critical exploits occur post-deployment—highlighting a structural visibility failure across the SDLC.
- Risk-Led Framework: A comprehensive checklist and maturity model for aligning technical findings to business impact, reducing remediation delays, and improving measurable security outcomes.
.webp)

.webp)